The original bug affected the gRPC and QUIC transports in CoreDNS. At a high level, the problem was that these transports checked whether a TSIG key name existed in the server configuration, but they did not actually verify the HMAC attached to the DNS message. That sounds like a small implementation detail, but in authentication […]
TL;DR Two Remote Code Execution (RCE) vulnerabilities were identified in datapizza-ai framework: What is datapizza-ai Source here https://github.com/datapizza-labs/datapizza-ai. CVE-2026-2969 The vulnerability is caused by the usage of vulnerable functions of Jinja2 template engine (datapizza-ai-core/datapizza/modules/prompt/prompt.py, source here https://github.com/datapizza-labs/datapizza-ai/blob/v0.0.2/datapizza-ai-core/datapizza/modules/prompt/prompt.py). To reproduce the exploit we have to install datapizza-ai: Create a python file with the following content: Execute […]
TL;DR A command injection vulnerability in the function tool run_ssh_command_with_credentials() available to AI agents in cai-framework
TL;DR https://github.com/hacktivesec/ghostwire Traditional pentesting distributions (and the Docker versions as well) have become heavy, hard to maintain, and inconsistent across different environments. Ghostwire was created to offer a simpler alternative: a minimal, repeatable, and transparent Docker toolkit with an essential set of tools for web, network, Active Directory, mobile, and post-compromise analysis. The project is […]
The Domino Effect: An Analysis of Catastrophic OPSEC Failures Through Aggregated Technical Lapses This research validates the thesis that major operational security (OPSEC) compromises are overwhelmingly the product of an accumulation of fundamental technical errors, rather than singular, indefensible exploits. Through in-depth forensic analysis of Ross Ulbricht, the FIN7 cybercrime syndicate, and Russian state-sponsored actors […]
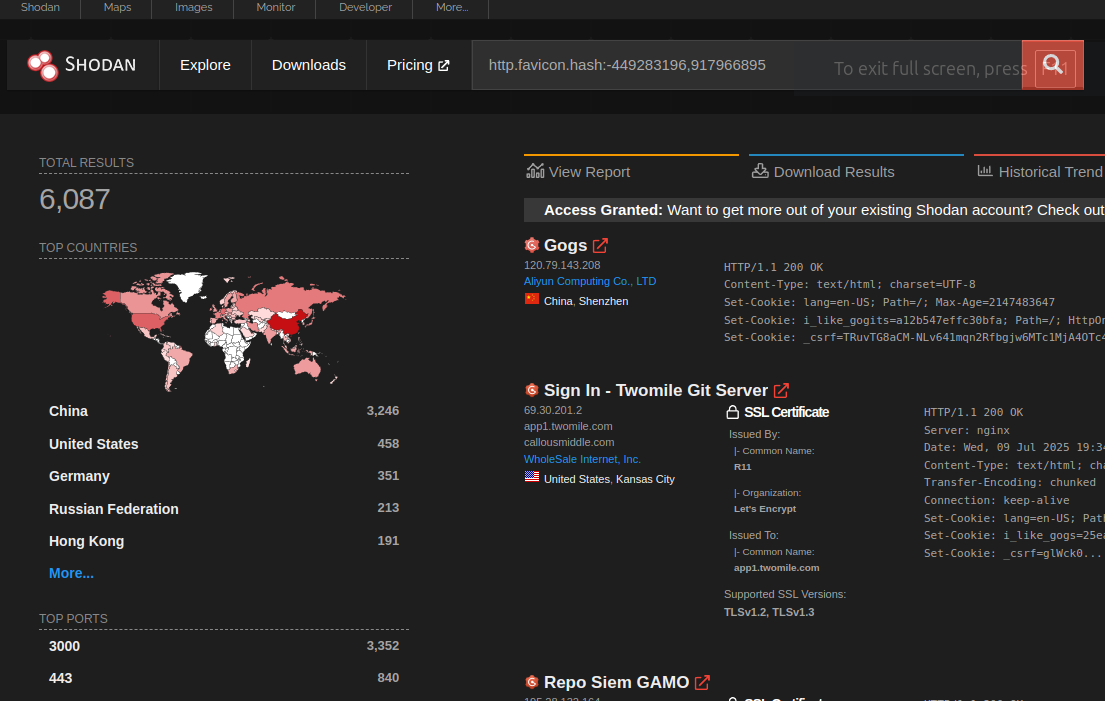
TL;DR Gogs is an open source self-hosted Git service. In the version 0.13.2 and prior, there is a stored Cross-Site Scripting (XSS) vulnerability, which allows client-side Javascript code execution. The vulnerability is caused by the usage of a vulnerable and outdated component: pdfjs-1.4.20 under public/plugins/. This issue has been fixed for gogs.io/gogs in version 0.13.3. […]
Non proverò a farvi tornare alla memoria la vostra infanzia da nerd, i primi computer o con quale software vi siete approcciati all’informatica (io non mi ricordo ad essere onesto, qualcosa come Bearshare o MSN…). Preferisco piuttosto parlare degli errori che ho fatto, cosa faccio oggi e dove spero di arrivare tra qualche anno. Buona […]
Introduction Effective cybersecurity relies not only on robust defense mechanisms but also on swift and coordinated incident response procedures. However, even well-prepared organizations can suffer critical failures if response protocols are not strictly followed. This article examines a real-world scenario where a Blue Team’s failure to act decisively during an ongoing cyberattack led to significant […]
TL;DR A Server-Side Template Injection (SSTI) vulnerability in spacy-llm
Introduction Serialization and deserialization mechanisms are always risky operations from a security point of view. In most languages and frameworks, if an attacker is able to deserialize arbitrary input (or just corrupt it as we have demonstrated years ago with the Rusty Joomla RCE) the impact is usually the most critical: Remote Code Execution. Without […]