The original bug affected the gRPC and QUIC transports in CoreDNS. At a high level, the problem was that these transports checked whether a TSIG key name existed in the server configuration, but they did not actually verify the HMAC attached to the DNS message. That sounds like a small implementation detail, but in authentication […]
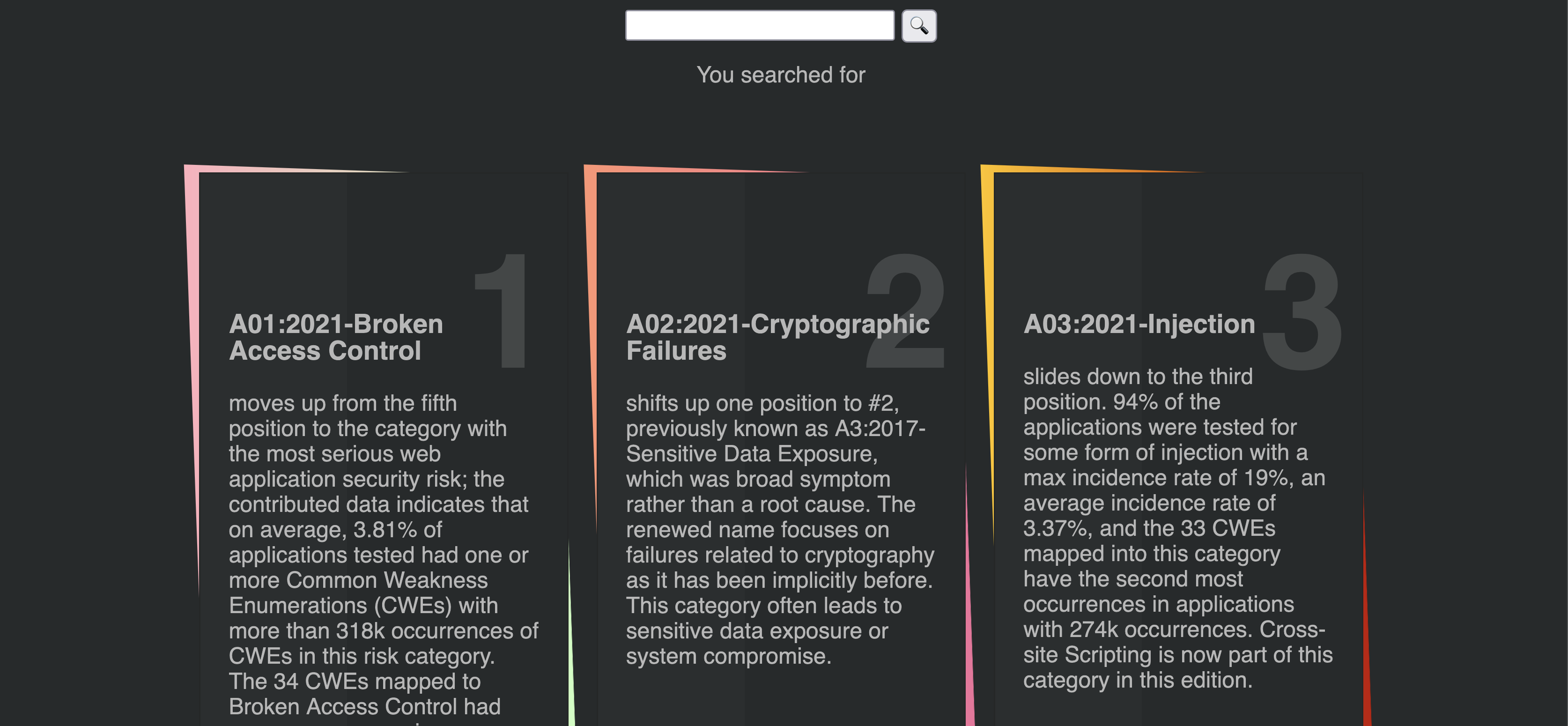
TL;DR Two Remote Code Execution (RCE) vulnerabilities were identified in datapizza-ai framework: What is datapizza-ai Source here https://github.com/datapizza-labs/datapizza-ai. CVE-2026-2969 The vulnerability is caused by the usage of vulnerable functions of Jinja2 template engine (datapizza-ai-core/datapizza/modules/prompt/prompt.py, source here https://github.com/datapizza-labs/datapizza-ai/blob/v0.0.2/datapizza-ai-core/datapizza/modules/prompt/prompt.py). To reproduce the exploit we have to install datapizza-ai: Create a python file with the following content: Execute […]
TL;DR A command injection vulnerability in the function tool run_ssh_command_with_credentials() available to AI agents in cai-framework
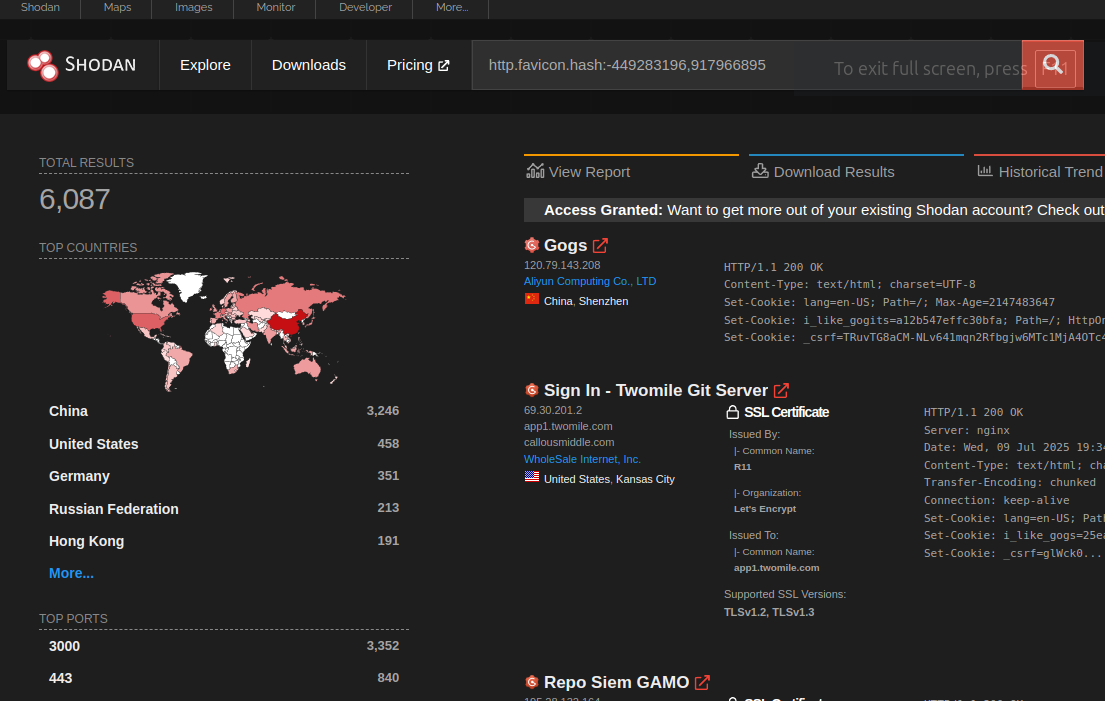
TL;DR Gogs is an open source self-hosted Git service. In the version 0.13.2 and prior, there is a stored Cross-Site Scripting (XSS) vulnerability, which allows client-side Javascript code execution. The vulnerability is caused by the usage of a vulnerable and outdated component: pdfjs-1.4.20 under public/plugins/. This issue has been fixed for gogs.io/gogs in version 0.13.3. […]
TL;DR A Server-Side Template Injection (SSTI) vulnerability in spacy-llm
TL;DR A Server Side Template Injection in changedetection.io caused by usage of unsafe functions of Jinja2 allows Remote Command Execution on the server host. Update changedetection.io to version 0.45.21 or later. A huge thanks to the mantainer (https://github.com/dgtlmoon) that was very responsive and collaborative to fix the issue, request a CVE number and inform the […]
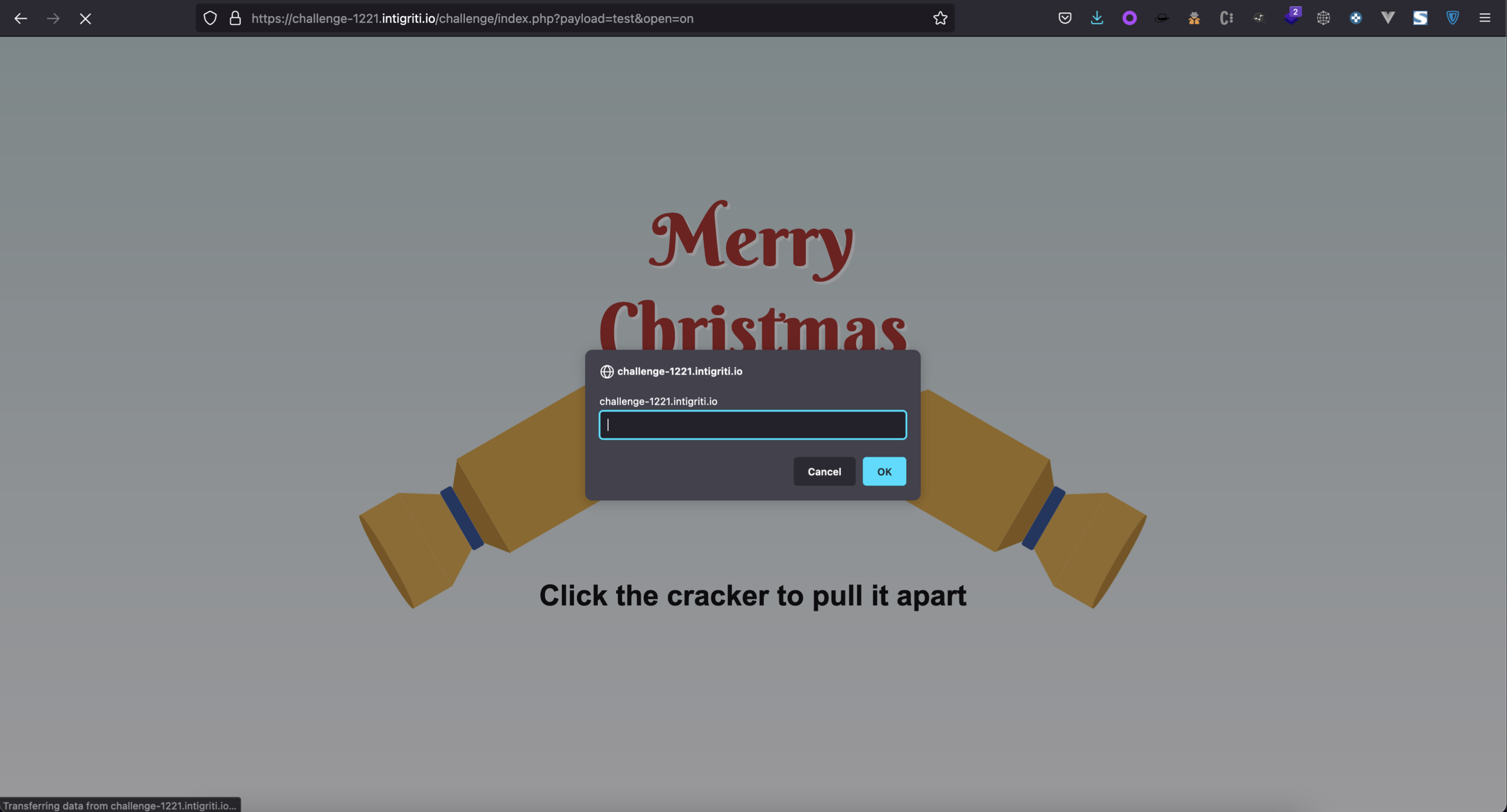
The approach to this challenge was completely different from the past two months, as the vulnerable component was on the backend, forcing us to approach it as a black box scenario. The page presents a simple submittable get form providing the open and payload parameters. To reach that from the UI, a user has to […]
The bug bounty program Intigriti hosts an XSS challenge every month. This time, the challenge was about bypassing CSP by reloading a VueJS instance, getting able to exploit a client side template injection. My solution can be summarized in 4 main steps: Finding reflection and achieving HTML Injection Accessing an abusable piece of code, containing […]
Preface As part of our recent research activity, we stumbled upon FormaLMS. The project is an open source Learning Management System built by forma.association and aimed at companies who want a learning platform for internal employees, partners, dealers and sellers. The project is opensource and could be downloaded from the main website: formalms.org and the […]
This is a brief story about how we found a vulnerability on a drupal plugin that, when not configured correctly, could allow an authenticated user to perform a privilege escalation attack on the Drupal platform. This plugin, as stated in the usage section of the drupal website, is used by roughly 522 websites in the […]
- 1
- 2